大数据分析下网络安全事件的预警

大数据分析下网络安全事件的预警(任务书,开题报告,论文11000字)
摘 要
许多网络攻击的前兆通常是侦察行动,通常称为扫描。本文将扫描检测问题形式化为一个数据挖掘问题。本文依托iMAP平台的数据处理能力,利用扫描时有规律向目的IP发送syn包、流量异常等特点,建立扫描行为模型,并编写识别规则。
对于本文所设计的规则,其现实意义并不是准确判断出每一条流是否是由扫描行为产生。而是通过大数据分析,当攻击者行为达到一定规模时,对部署网络造成一定威胁,进行告警,提醒管理者及时处理与解决。其中外网对内网地址的扫描主要关注攻击流量是否会影响内网正常通信。告警内网地址对外网扫描是为了提醒管理者内网地址是否已经中病毒或已被攻击者控制。
本文对设计的规则进行了真实数据的测试,并对测试结果进行了检测。检测结果表明了本文设计规则对扫描行为的告警有效且存在一定现实意义。
关键词:大数据分析 网络安全 扫描 告警
Network security event warning based on big data analysis
Abstract
The precursor to many cyber attacks is often reconnaissance, often called scanning.This paper formalizes the problem of scanning detection into a data mining problem.Based on the data processing capacity of iMAP platform, this paper establishes the scanning behavior model and writes the recognition rules by taking advantage of the characteristics of sending syn packets and traffic anomalies to the destination IP from time to time.
For the rules designed in this paper, its practical significance is not to accurately determine whether each stream is generated by scanning behavior.However, through big data analysis, when the behavior of the attacker reaches a certain scale, it will pose a certain threat to the deployed network, and warn the manager to timely deal with and solve the problem.Among them, the scanning of the internal network address by the external network mainly focuses on whether the attack traffic will affect the normal communication of the internal network.Warning internal network address external network scanning is to remind the administrator whether the internal network address has been in the virus or has been under the control of the attacker.
This paper tests the real data of the designed rules and tests the test results.The results show that the proposed rules are effective and have some practical significance in alerting the scanning behavior.
Key Words: Big Data Analysis; Network Security; Scan; Alarm [资料来源:http://Doc163.com]
[版权所有:http://DOC163.com]
目 录
第一章 引言………………………………………………………………………1
1.1 课题来源及意义……………………………………………………………1
1.2 国内外的研究和发展现状…………………………………………………2
第二章 端口扫描…………………………………………………………………3 [资料来源:http://doc163.com]
2.1 定义…………………………………………………………………………3
2.2 端口扫描的分类……………………………………………………………3
2.3 扫描行为特征………………………………………………………………6
2.3.1流量异常……………………………………………………………6
2.3.2 TCP状态分析………………………………………………………7
[资料来源:http://Doc163.com]
2.3.3 TCP状态值…………………………………………………………9
第三章 规则设计………………………………………………………………11
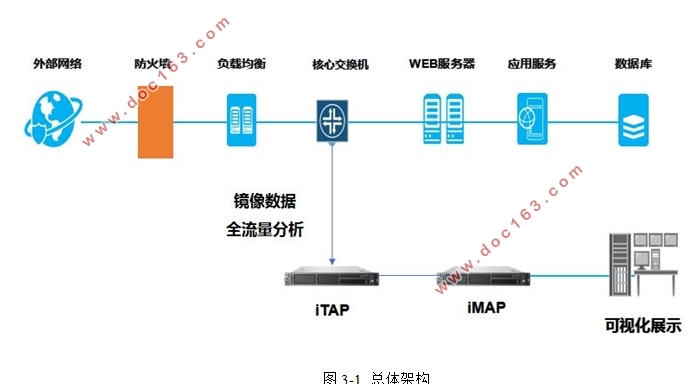
3.1 平台介绍…………………………………………………………………11
3.2 外网扫描规则……………………………………………………………12
3.3 内网扫描规则……………………………………………………………15 [资料来源:http://Doc163.com]
3.4 章节总结…………………………………………………………………19
第四章 实验检测………………………………………………………………20
4.1 内网发起的扫描…………………………………………………………20
4.1.1 SYN扫描行为………………………………………………………20
4.1.2 针对固定端口的扫描………………………………………………23
4.1.3 针对固定IP的扫描………………………………………………24
[资料来源:http://doc163.com]
4.2 外网向内网发起的扫描…………………………………………………26
4.3 章节总结…………………………………………………………………29
第五章 总结与展望…………………………………………………………30
参考文献…………………………………………………………………………31
致谢………………………………………………………………………………32
